The syslog-ng Store Box (SSB) appliance is built on syslog-ng Premium Edition (PE). SSB inherits most of syslog-ng PE’s features and makes them available with an easy-to-use graphical user interface. One of the typical use cases for SSB (and syslog-ng PE) is optimizing the logging infrastructure for SIEM / log analysis. Two recently introduced SSB destinations for log analytics are Splunk HEC (HTTP Event Collector) and Microsoft Sentinel.
The syslog-ng Store Box appliance can collect log messages from many different log sources, in many formats. These include UNIX / Linux / Windows system logs, firewall and router logs, various application logs, and now SQL sources as well. SSB can parse, rewrite, filter, and store log messages. In addition to the traditional syslog-ng features, the SSB appliance provides an interface to search log messages, and does complete log life cycle management, including archiving and backup. Finally, it can also forward events to various on-prem and cloud destinations. It allows you to optimize your SIEM installations both for resources and licensing, as you can collect log messages in a single step, store them on SSB, and only forward a reduced subset of logs to various analytics tools.
Before you begin
Version 6.6 of the SSB appliance was the first one to support the Splunk destination, and version 6.7 was the first to support the Sentinel destination. However, both features received performance and bug fixes, even minor feature enhancements since the original feature releases. Thus, it is recommended to always use the latest feature release. If you do not have SSB yet, download the 30 day free trial at https://www.syslog-ng.com/register/115581/
Configuring and testing SSB
Once you have SSB up and running, adding a Splunk HEC or a Sentinel destination and doing basic configuration is easy. Before doing the actual configuration, you must collect some crucial information from your Splunk and / or Sentinel administrator.
For Sentinel, these are the Workspace ID and the Auth Secret.
For Splunk, these are the Token, index name and URL.
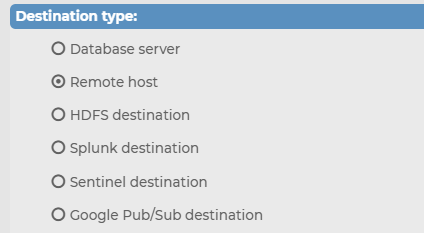
This is the bare minimum information you need to get started. With the information at hand, you are ready configure SSB. Log in as an administrator. Go to the Log menu and select Destinations. By default, Remote Host is selected, which stands for a remote syslog destination. Depending on your environment, click on Splunk or Sentinel:
Enter the information you collected earlier into the relevant fields. Do not forget to give your freshly created destination a name. Once ready, click on Commit to save.
You are now almost ready for initial testing. You now have a new destination, but it is not connected anywhere. For that, you have to add it to a log path. When you install syslog-ng, there is a preconfigured log path that collects all logs coming in from the network to a destination called Center. You can add your freshly created destination below Center. From the drop-down list, select the name of the freshly created destination.
Once you have committed the changes, you are ready for initial testing. For testing, you also need some log messages. You can direct a syslog-ng client to one of the network sources of SSB or use the loggen utility of syslog-ng to generate log messages.
If you expect to forward only at a low message rate, the default configuration is perfect. However, if you expect a higher message rate (over 10k events a second), it is worthwhile to do some performance tuning. You can set the number of parallel connections, the number of messages sent at once, and in case of Splunk, you can also configure multiple destination URLs. In this case, syslog-ng will automatically load-balance log messages among the URLs without any further software components.
What is next?
If you want to give the Splunk HEC or Sentinel destination of SSB a try, watch our webcast at https://www.syslog-ng.com/webcast-ondemand/forwarding-to-sentinel-and-splunk-hec-with-ssb/ which helps you to set up a test environment and shows you the Splunk and Sentinel destinations in action. It also gives you a good introduction to SSB.


