Optimizing SIEM
Security Information and Event Management (SIEM) solutions form the core of many enterprises’ IT Security strategy but they can be expensive to deploy and maintain. Optimizing your SIEM solution can reduce costs and improve performance.
 02:35
02:35
Challenges
Data reliability issues
Companies struggle to make sense of log data received in varying formats. Unreliable collection can lead to incomplete data.
High TCO
SIEM solutions are often very expensive to purchase, implement and maintain both in terms of financial investment and internal resources.
Performance issues
Large networks produce massive amounts of logs from a wide variety of devices and applications. Many SIEMs become overloaded with data, leading to searches that take hours.
Scalability issues
IT networks are continually growing both in terms of the amount of log sources and log data. Extending current solutions can be difficult and expensive.
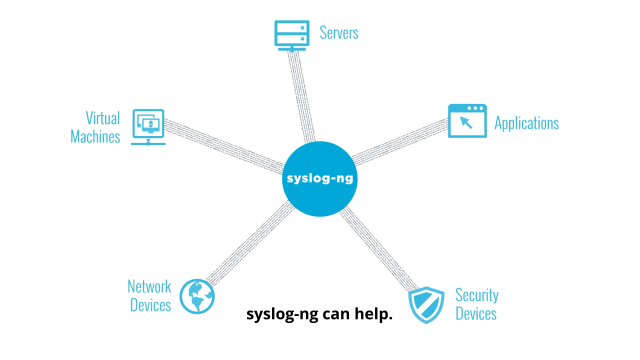
Why syslog-ng?
Distributed pre-processing
syslog-ng can filter and normalize log data on clients at unparalleled speed to reduce the size and complexity of log data stored centrally. Filtering unimportant log messages that do not need to be analyzed also reduces the load on the SIEM, saving both processing power and license costs.
Reliable log transfer
syslog-ng can ensure zero message loss during transport from clients to the central log server using TCP for transmission, the Reliable Log Transfer Protocol (RLTP ™) for application acknowledgment, a client-side disk buffer, and client-side failover for network outages.
Centralized collection
syslog-ng can be installed on over 50 platforms including a wide variety of Linux, UNIX, HP, IBM, Microsoft Windows, and Solaris variations
Tamper-proof transfer and storage
syslog-ng uses SSL/TLS encryption to transfer logs and store them in an encrypted, compressed and time-stamped log store.
Benefits
Better SIEM performance
Reducing the size and complexity of log data can dramatically improve search times. Using granular policies based on log file types and compliance requirements, retention and detection can be achieved easily and reliably.
Higher quality data
Tamper proof, secure logs in their raw format provide legally admissible evidence.
Increased confidence in analytics
Being certain that logs aren’t missing or haven’t been tampered with increases the confidence in the results of SIEM.