syslog-ng Premium Edition
 02:35
02:35
Optimize your SIEM with syslog-ng
Key features
Secure transfer and storage
Have confidence in the data underlying your analytics, forensics and compliance efforts.
Using local disk buffering, client-side failover and application layer acknowledgement, syslog-ng can transfer logs with zero message loss. Encrypted transfer and storage ensure logs cannot be tampered with, preserving the digital chain of custody.
Reliable log transfer
syslog-ng Premium Edition can send and receive log messages in a reliable way over the TCP transport layer using the Advanced Log Transfer Protocol™ (ALTP™).
ALTP™ is a new transport protocol that prevents message loss during connection breaks.
Secure Transfer using TLS
Log messages may contain sensitive information that should not be accessed by third parties. Therefore, syslog-ng Premium Edition uses the Transport Layer Security (TLS) protocol to encrypt the communication.
TLS also allows the mutual authentication of the host and the server using X.509 certificates.
Secure, Encrypted Log Storage
syslog-ng Premium Edition can store log messages securely in encrypted, compressed, indexed and timestamped binary files, so any sensitive data is available only for authorized personnel who have the appropriate encryption key.
Timestamps can be requested from external timestamping authorities.
Scalable architecture
Scale up your log management
Depending on its configuration, one syslog-ng server can collect more than half a million log messages per second from thousands of log sources.
A single central server can collect log messages from more than 5,000 log source hosts. When deployed in a client relay configuration, a single syslog-ng log server can collect logs from tens of thousands of log sources.
Extreme message rate collection
The syslog-ng application is optimized for performance, and can handle an enormous amount of messages.
Depending on its exact configuration, it can process over half a million messages per second in real-time, and over 24 GB of raw logs per hour on standard server hardware.
Collection from thousands of sources
Easy monitoring
syslog-ng allows you to granularly select which statistics of syslog-ng you want to monitor. The statistics are available as structured name-value pairs, so you can format the output similarly to other log messages.
That way, you can easily convert the statistics and metrics and send the results into your enterprise monitoring solution (for example, IBM Tivoli Netcool, Riemann, Redis, or Graphite).
Scaling to large networks with syslog-ng
This short video will show you how syslog-ng scales to the largest IT environments, ensuring your log infrastructure can reliably and securely collect and manage log data.
Flexible log routing
Reduce maintenance and deployment costs with universal collection
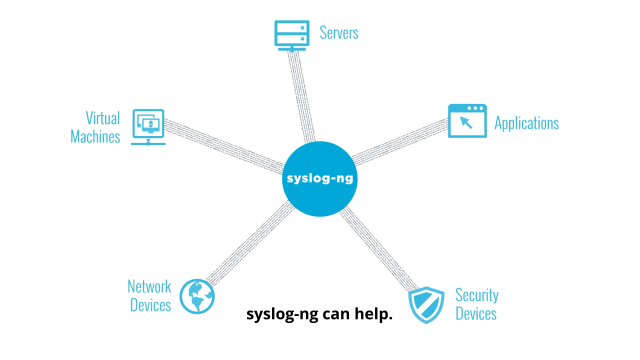
syslog-ng can be deployed as an agent on a wide variety of hosts and flexibly route logs to multiple analytic tools or databases, eliminating the need to deploy multiple agents on servers.
Tested binary files for the syslog-ng Premium Edition are available for more than 50 server platforms, reducing the time required for installation and maintenance.
Collect from a wide variety of sources, including Windows
syslog-ng Premium Edition can natively collect and process log messages from SQL databases, enabling users to easily manage log messages from a wide variety of enterprise software and custom applications.
The syslog-ng Agent for Windows is an event log collector and forwarder application for Microsoft Windows platforms.
Read log messages from any text file
Some applications use many different log files, and sometimes these files are not even located in the same folder. Automatically generated file and folder names are also often a problem.
To solve these issues, the filenames and paths specifying the log files read by syslog-ng can include wildcards, and syslog-ng can automatically scan entire subfolder trees for the specified files.
The syslog-ng Premium Edition application is also able to process multi-line log messages, for example, Apache Tomcat messages.
Forward to multiple destinations
Many large organizations need to send their logs to multiple log analysis tools. Different groups, including IT operations, IT security and corporate risk and governance, need access to the same log data but have different log analysis goals and tools.
The syslog-ng application can send logs directly to SQL databases, MongoDB and Hadoop Distributed File System (HDFS) nodes, or use the Standard Network Management Protocol (SNMP) and Simple Mail Transfer Protocol (SMTP) for other destinations.
Real time transformation
Optimize your tools with distributed processing
With powerful filtering, parsing, re-writing and classification options, syslog-ng can transform logs on remote hosts, reducing the amount and complexity of log data forwarded to analytic tools like SIEM or APM, reducing their total cost of ownership.
The flexible configuration language allows users to construct powerful, complex log processing systems on remote hosts with simple rules.
Filter, parse, re-write
syslog-ng can sort the incoming log messages based on their content and various parameters like the source host, application, and priority. Directories, files, and database tables can be created dynamically using macros.
Complex filtering using regular expressions and boolean operators offers almost unlimited flexibility to forward only the important log messages to the selected destinations.
Real time classification
By comparing log messages to known patterns, syslog-ng is able to identify the exact type of the messages, and sort them into message classes. The message classes can then be used to classify the type of the event described in the log message.
The message classes can be customized, and for example can label the messages as user login, application crash, file transfer, etc. events.
Enrich
syslog-ng can use an external database file to append custom name-value pairs to incoming logs, thus extending, enriching, and complementing the data found in the log message.
You can also correlate and aggregate information from log messages using a few simple filters that are similar to SQL GROUPBY statements.